Field Name | Field Type | Description |
|---|
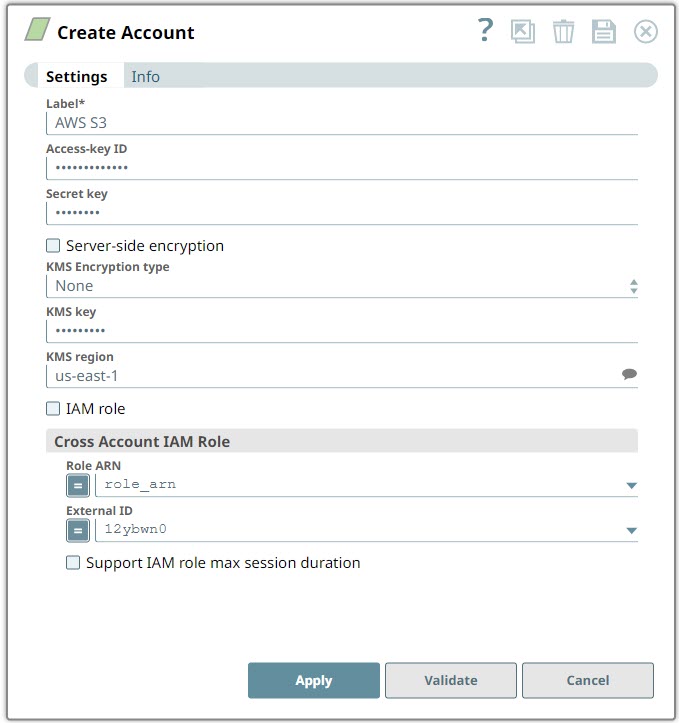
Label* Default Value: None
Example: AWS S3 Account | String | Specify a unique name for the account instance |
Access-key ID Default value: [None]
Example: <Encrypted>
| String | Specify a unique access key ID part of AWS authentication. The Access-key ID is required when the IAM role is disabled. |
|
Secret key Default value: [None]
Example: <Encrypted>
| String | Specify the secret key part of AWS authentication The Secret key is required when the IAM role is disabled. |
|
Server-side encryption Default Value: Deselected | Checkbox | If selected, the S3 file is written and encrypted using the 256-bit Advanced Encryption Standard AAES256. For Snaps that read objects from S3, this field is not required, as encrypted data is automatically decrypted when data is read from S3. |
KMS Encryption type Default Value: None
Example: Server-Side KMS Encryption | String | Choose the encryption type from the following list. This field represents the AWS Key Management Service key used to encrypt S3 objects—it can be the key ID or ARN. None: The files do not get encrypted using KMS encryption. Server-Side KMS Encryption: The output files on Amazon S3 are encrypted with Amazon S3 generated KMS key. Client-Side KMS Encryption: The output files on Amazon S3 are encrypted with client generated KMS key.
noteFor Snaps that write objects to S3, this is required for encryption types—Server-Side encryption and Client-Side encryption with AWS KMS-Managed Keys. For Snaps that read objects from S3, this field is not required. For Server-Side encryption, the key must be in the same region as the S3 bucket. For Client-Side encryption, a key from any region can be used by using the key ARN value. If a key ID is used for Client-Side encryption, it defaults to the us-east-1 region.
For Snaps that write objects to S3, this is required for encryption types—Server-Side encryption and Client-Side encryption with AWS KMS-Managed Keys. For Snaps that read objects from S3, this field is not required. For Server-Side encryption, the key must be in the same region as the S3 bucket. For Client-Side encryption, a key from any region can be used by using the key ARN value. If a key ID is used for Client-Side encryption, it defaults to the us-east-1 region.
|
KMS key Default Value: N/A
Example: <Encrypted> | String | Specify the AWS Key Management Service (KMS) key ID or ARN to be used for the S3 encryption. This is only required if the KMS Encryption type property is configured to use the encryption with KMS. Learn more about the KMS key: AWS KMS Overview and Using Server Side Encryption. noteFor Snaps that write objects to S3 using Server-Side encryption and Client-Side encryption with AWS KMS-Managed Keys this is required. For Snaps that read objects from S3, this field is not required. For Server-Side encryption, the key must be in the same region as the S3 bucket. For Client-Side encryption, a key from any region can be used by using the key ARN value. If a key ID is used for Client-Side encryption, it defaults to the us-east-1 region.
For Snaps that write objects to S3 using Server-Side encryption and Client-Side encryption with AWS KMS-Managed Keys this is required. For Snaps that read objects from S3, this field is not required. For Server-Side encryption, the key must be in the same region as the S3 bucket. For Client-Side encryption, a key from any region can be used by using the key ARN value. If a key ID is used for Client-Side encryption, it defaults to the us-east-1 region.
|
KMS region Default Value: N/A
Example: s3.us-east-2 | String | Specify or select a name of the region to which the KMS key belongs. |
IAM role
Default Value: Deselected
| Checkbox | Select this checkbox to use the Groundplex EC2 instance stored in the IAM role, instead of the normal AWS authentication to access the S3 bucket. The Access-key ID and Secret key fields are ignored in this case. Learn more about Configuring an EC2 role for IAM Role in AWS S3 Account. noteThe List, Read and Write permissions are required as per the attached S3 policy for the IAM role stored on the EC2 instance. The IAM role is valid only in Groundplex nodes hosted in the EC2 environment, and also requires specific configuration. Set the global.properties file on the Groundplex as shown below and restart the JCC:
jcc.jvm_options = -DIAM_CREDENTIAL_FOR_S3=TRUE When you select the IAM Role checkbox, the validation of the account is not supported.
The List, Read and Write permissions are required as per the attached S3 policy for the IAM role stored on the EC2 instance. The IAM role is valid only in Groundplex nodes hosted in the EC2 environment, and also requires specific configuration. Set the global.properties file on the Groundplex as shown below and restart the JCC:
jcc.jvm_options = -DIAM_CREDENTIAL_FOR_S3=TRUE When you select the IAM Role checkbox, the validation of the account is not supported.
|
Cross Account IAM Role | Use this field set to configure the cross account access. Learn more about setting up Cross Account IAM Role. |
Role ARN Default Value: None
Example: arn:aws:s3::test-bucket-sa-sl/* | String/Expression | Specify the Amazon Resource Name of the role to assume. |
External ID Default Value: None
Example: 321f248c-8f4a-21be-87c4-184c9f8e2d03 | String/Expression | Specify an external ID that might be required by the role to assume. |
Support IAM role max session duration
Default Value: Deselected
| Checkbox | Select this checkbox when you want to extend the maximum session duration of an IAM role defined in AWS. On selecting this checkbox, the cross-account IAM role is assumed with the maximum session duration defined for the IAM role. This checkbox is deselected by default. The default maximum session duration for an IAM role is one hour; however, you can define a custom duration between 1-12 hours. Learn how to increase the IAM role maximum session duration limit.
We recommend that you select this checkbox if the maximum session duration of the IAM role is greater than an hour. |
|
 ): Indicates a list that is dynamically populated based on the configuration.
): Indicates a list that is dynamically populated based on the configuration. ): Indicates whether the value is an expression (if enabled) or a static value (if disabled). Learn more about Using Expressions in SnapLogic.
): Indicates whether the value is an expression (if enabled) or a static value (if disabled). Learn more about Using Expressions in SnapLogic. ): Indicates that you can add fields in the field set.
): Indicates that you can add fields in the field set. ): Indicates that you can remove fields from the field set.
): Indicates that you can remove fields from the field set.