...
On this page
| Table of Contents | ||||||
|---|---|---|---|---|---|---|
|
Overview
You can
...
- Your private project folder: This folder contains the pipelines that will use the account.
- Your Project Space’s shared folder: This folder is accessible to all the users that belong to the Project Space.
- The global shared folder: This folder is accessible to all the users within an organization in the SnapLogic instance.
Prerequisites
Valid permissions based on the Snap and intended operation. See the Account Permissions the section below for more information.
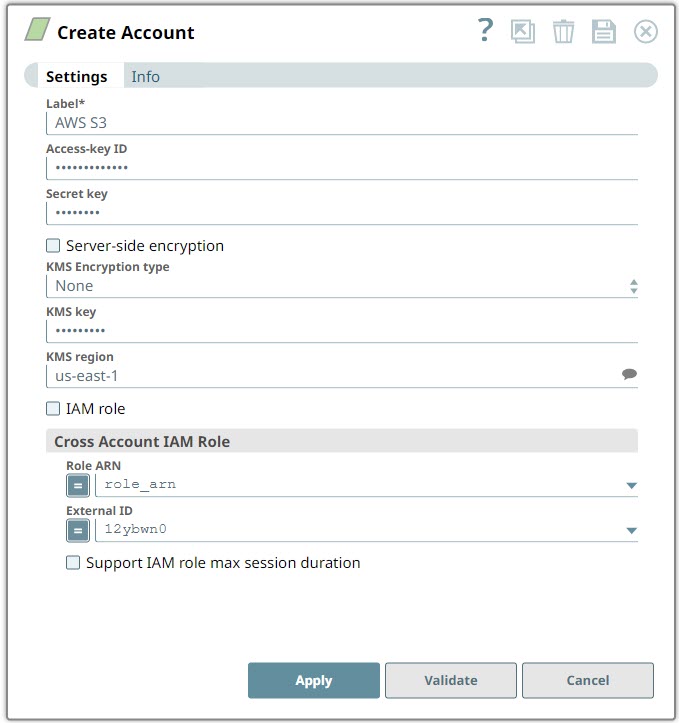
Account Settings
...
Label
...
use the AWS S3 account to connect the Binary Snaps with data sources that are in AWS S3.
Prerequisites
Valid permissions based on the Snap and intended operation.
Account Settings
...
| Info |
|---|
|
...
Field Name | Field Type | Description | |
|---|---|---|---|
Label* | String | Specify a unique name for the account instance | |
Access-key ID | |||
...
Default value: [None] | String | Specify a unique access key ID part of AWS authentication.
| |||
Secret key Default value: [None] | |||||
...
String |
...
Specify the secret key part of AWS authentication |
...
| |||
Server-side encryption Default value: Not Selected | Checkbox | If selected, the S3 file is written and encrypted using the 256-bit Advanced Encryption Standard AAES256. For Snaps that read objects from S3, this field is not required, as encrypted data is automatically decrypted when data is read from S3. | |
KMS Encryption type Default value: | |||
...
[None] | String | Choose the encryption type from the following list. This field represents the AWS Key Management Service key used to encrypt S3 | |
...
objects—it can be the key ID or ARN.
|
...
|
...
|
...
For Snaps that read objects from S3, this field is not required.
The available options are:
...
|
...
KMS |
...
key |
...
...
Default value: [None] |
...
String |
...
Specify the AWS Key Management Service (KMS) key ID or ARN |
...
to be used for the S3 encryption. This is only required if the KMS Encryption type property is configured to use the encryption with KMS. |
...
Learn more |
...
about the KMS key |
...
...
and Using Server Side Encryption.
|
...
|
...
|
For Snaps that read objects from S3, this field is not required.
Default value: [None]
KMS region Default Value: N/A | String | Specify or select a name of the region to which the KMS key belongs. | |
...
IAM role | Checkbox | If selected, the IAM role stored in the EC2 instance is used, instead of the normal AWS authentication, to access the S3 bucket. The Access-key ID and Secret key fields are ignored in this case. To create EC2 role, see Configuring an EC2 role for IAM Role in AWS S3 Account.
| |||
...
|
...
| |
Cross Account IAM Role |
...
Use this field set |
...
to configure the cross account access |
...
- Role ARN
- External ID
...
. Learn more about setting up Cross Account IAM Role. | ||
Role ARN | ||
...
Default value: [None] | String/Expression | Specify the Amazon Resource Name of the role to assume. |
External ID Default value: [None] |
...
| String/Expression | Specify an external ID that might be required by the role to assume. |
Default value: [None]
Support IAM role max session duration
| Checkbox | Select this checkbox when you want to extend the maximum session duration of an IAM role defined in AWS. On selecting this checkbox, the cross-account IAM role is assumed with the maximum session duration defined for the IAM role.
| ||
...
| icon | false |
|---|
|
...
Default Value: Deselected
Account Encryption
...
If you are using Standard Encryption, the High sensitivity settings under Enhanced Encryption are followed.
...
If you have the Enhanced Account Encryption feature, the following describes which fields are encrypted for each sensitivity level selected per each account.
- High: Access-key ID, Secret Key
- Medium + High: Access-key ID, Secret Key
- Low + Medium + High: Access-key ID, Secret Key
Troubleshooting
Error | Reason | Resolution |
|---|---|---|
When creating an S3 account, if you select the IAM role checkbox, then the following error is displayed on clicking the Validate button.
| When you select the IAM role checkbox and validate the account, an error is displayed. | Ensure that you provide valid Role ARN and External ID values and then click Apply instead of Validate (on the AWS S3 account settings dialog) to use the account. |
| Multiexcerpt macro | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
Account Permissions
See Setting Permissions and Permissions for the Amazon S3 Bucket for more information. |
ACL permissions
ACL permission | Corresponding access policy permissions when the ACL permission is granted on a bucket | Corresponding access policy permissions when the ACL permission is granted on an object |
|---|---|---|
|
|
...
and |
|
...
and | |
|
|
...
|
...
In addition, when the grantee is the bucket owner, |
...
granting |
...
permission in a bucket ACL allows |
...
the |
...
action to be performed on any version in that bucket. | Not applicable. | |
|
|
|
...
and | ||
|
|
|
...
and | |
| Equivalent to |
...
granting |
...
and |
...
ACL permissions. Accordingly, this ACL permission maps to a combination of corresponding access policy permissions. | Equivalent to |
...
granting |
...
and |
...
ACL permissions. Accordingly, this ACL permission maps to a combination of corresponding access policy permissions. |
...
| Insert excerpt | ||||||||
|---|---|---|---|---|---|---|---|---|
|