On this page
| Table of Contents | ||||
|---|---|---|---|---|
|
Introduction
Single Sign On Single Sign On is a convenient way for users to log into multiple services without needing to enter their username and password for each service. SnapLogic supports Single Sign On SnapLogic supports Single Sign On (SSO) through the Security Assertion Markup Language Security Assertion Markup Language (SAML 2.0) standard. If If you are using a SAML-2 compatible Identity Provider (IdP) to perform SAML authentication, you can configure your SnapLogic organization to authenticate users against your IdP. If you disable password-based login, users will have to use SSO. If you leave password-based login enabled, users can choose basic authentication or SSO to log in. You can use multiple IdPs, but only a single IdP can be configured per Org.
SnapLogic certifies the following IdPs as compatible with our platform:
- OpenAM
- Microsoft Entra ID
- Okta
- Ping
| Info |
|---|
Members of an SSO-enabled Org might need to log into a different Org, such as one provided by SnapLogic for training or product trials. In this case, the account in the Org without SSO should be created using a different email address. |
...
The SAML standard defines how Service Providers, in this case, the SnapLogic Platform, communicate with Identity Providers (IdP) to securely authenticate users. You must first create an application integration in your IdP that will handle authorization for all of your SnapLogic Orgs. After After you create the application integration in your IdP, export the metadata and import it into all of your SnapLogic Orgs using Classic Manager or Admin Manager.
The communication between the SnapLogic Platform and the IdP starts after the user clicks the Single Sign On link from the SnapLogic login screen. The user enters an Org name and clicks Log in. The request destination is defined in the SSO configuration. The SnapLogic Platform sends a SAML request to the IdP application integration that you created for SnapLogic. The request contains an AssertionConsumerServiceURL element that specifies where the response should be sent. The IdP ensures that the AssertionConsumerServiceURL is associated with the requester. To make this possible, you must add the Reply URLs for all of your the configured SnapLogic Orgs to the IdP application integration.
You can set up environments to have different IdPs. An SSO login gives users access to all environments configured for the same IdP where they have an account. For example, if a user is a member of Env_1 and Env_2 and they log into Env_1 with SSO, they can switch to Env_2 without logging in again. This is assuming that both environments have the same IdP provider configured. If they also have an account on Env_3 and it uses a different IdP, they need to log out and log in using that IdP to access Env_3.
Configuration
Configuration takes place in both your IdP and in the SnapLogic Platform. You must have Org admin access to configure SSO.
...
If your company has multiple SnapLogic Orgs that will use the same IdP, use the metadata from one Org to set up one IdP Application Integration.
- Choose one of your SnapLogic Orgs to provide the metadata for the IdP Application Integration. It doesn't matter which Org you choose, however, any user who wants to use SSO to sign in must be a member of this Org.
- Log into that SnapLogic Org and do the following:
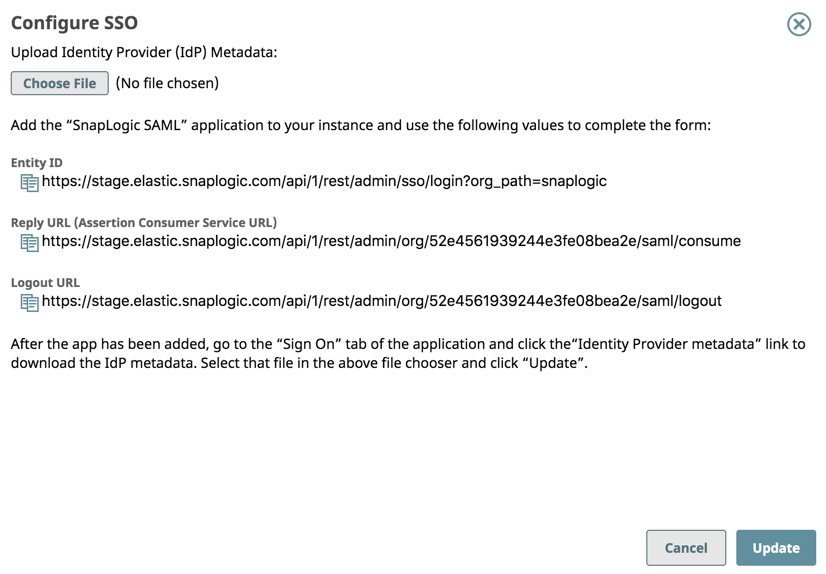
- Click Configure SSO. The dialog opens.
- Copy the Entity ID, Reply URL, and Logout URL to a text file. You will need them when creating your IdP application integration. Note that your IdP might use a different name for these URLs. For example, the SnapLogic Reply URL value goes into the Okta Single sign-on URL field.
- Click Configure SSO. The dialog opens.
- Log into the remaining SnapLogic Orgs and do the following:
- Click Configure SSO. The dialog opens.
- Copy the Reply URL to a text file that you created in Step 2b. Note that the Reply URL contains the Org ID, not the Org name.
- Log into your IdP and create one application integration for SnapLogic access:
- Provide the Entity ID, Reply URL, and Logout URL for the Org that you chose in step 1.
- Provide the Reply URLs that you copied in step 3b to the list of Reply URLs in the IdP’s application integration
- Export the metadata from the IdP application integration. In some IdPs, such as Okta, provide a URL instead of a download button. You can open the URL in a new browser tab to view and save the XML.
- Save the exported metadata on your machine to use when configuring your SnapLogic Orgs.
...
Use the metadata from the IdP Application Integration for SnapLogic to configure SSO on all of your Orgs that should use that IdP.
- Log into the Org you used to provide the Entity ID, Reply URL, and Logout URL for the IdP Application Integration.
- In SnapLogic Manager, click Settings in the main menu on the left. The Organization Settings page opens.
- Scroll down and click Configure SSO.
- Click Choose File and navigate to the metadata file from your IdP that you saved previously.
Click Update to upload the metadata.
When the upload finishes, the SnapLogic server validates the metadata and updates the Settings page to reflect the new values.Note Double-check the values to ensure that they refer to your IdP.
- Repeat Steps 2 -5 for all Orgs.
...