...
In this article
| Table of Contents | ||||||
|---|---|---|---|---|---|---|
|
You can create an account with the Designer or Manager. In Designer, when working on pipelines, every Snap that needs an account prompts you to create a new account or use an existing account. The accounts can be created in or used from:
...
Overview
You can use the AWS S3 account to connect the Binary Snaps with data sources that are in AWS S3.
Prerequisites
Valid permissions based on the Snap and intended operation.
...
Account Configuration
In Manager, you can navigate to the required folder and create an account in it (see Accounts). To create an account for binary files:
- Click Create, then select Binary, then AWS S3.
- Supply an account label.
Supply the necessary information.
- (Optional) Supply additional information on this account in the Notes field of the Info tab.
- Click Apply.
Account Settings
...
...
...
Label
...
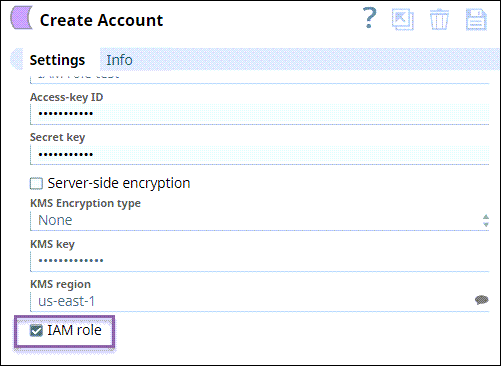
EC2 instance as a Groundplex. The IAM role is valid only in Groundplex nodes hosted in the EC2 environment. Learn more about Configuring an EC2 role for IAM Role in AWS S3 Account.
JCC with the following global property set:jcc.jvm_options=-DIAM_CREDENTIAL_FOR_S3=TRUE
If you do not have an EC2 instance groundplex, then you can authenticate your account by using the Access Key ID and Secret Key. You can assume roles using the Cross account IAM role, that uses the IAM role specified in the settings. The Access Key ID and Secret Key need to have the ability to assume in the user specifications.
Account Settings
...
| Info |
|---|
|
Field Name | Field Type | Description | |
|---|---|---|---|
Label* Default Value: None | String | Specify a unique name for the account instance | |
Access-key ID | |||
...
Default value: [None] | String | Specify a unique access key ID part of AWS authentication.
| |||
Secret key Default value: [None] | |||||
...
Secret key
Example: <Encrypted> | String | Specify the secret key part of AWS authentication | |
...
| |||
Server-side encryption Default Value: Deselected | Checkbox | If selected, the S3 file is written and encrypted using the 256-bit Advanced Encryption Standard AAES256. For Snaps that read objects from S3, this field is not required, as encrypted data is automatically decrypted when data is read from S3. | |
KMS Encryption type Default | |||
...
Value: |
...
None | String | Choose the encryption type from the following list. This field represents the AWS Key Management Service key used to encrypt S3 | |
...
objects—it can be the key ID or ARN.
|
...
|
...
|
For Snaps that read objects from S3, this field is not required.
The available options are:
KMS key |
...
Default value: [None]
...
Default Value: N/A | String | Specify the AWS Key Management Service (KMS) key ID or ARN | |
...
to be used for the S3 encryption. This is only required if the KMS Encryption type property is configured to use the encryption with KMS. |
...
Learn more |
...
about the KMS key |
...
...
and Using Server Side Encryption.
|
...
|
...
|
For Snaps that read objects from S3, this field is not required.
Default value: [None]
...
KMS region Default Value: N/A | String | Specify or select a name of the region to which the KMS key belongs. | |
Example: s3.us-east-2
...
IAM role
| Checkbox | Select this checkbox to use the Groundplex EC2 instance stored in the IAM role, instead of the normal AWS authentication | |
...
to access the S3 bucket. The Access-key ID and Secret key fields are ignored in this case. |
...
Learn more about Configuring an EC2 role for IAM Role in AWS S3 Account.
|
...
|
...
|
...
|
...
|
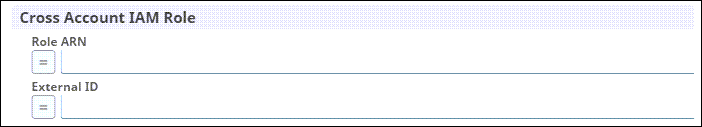
Cross Account IAM Role |
...
Use this field set |
...
to configure the cross account access |
...
- Role ARN
- External ID
...
. Learn more about setting up Cross Account IAM Role. | ||
Role ARN | ||
...
Default Value: None | String/Expression | Specify the Amazon Resource Name of the role to assume. |
External ID Default |
...
Value: None | String/Expression | Specify an external ID that might be required by the role to assume. |
Support IAM role max session duration
| ||
...
Account Encryption
...
If you are using Standard Encryption, the High sensitivity settings under Enhanced Encryption are followed.
...
If you have the Enhanced Account Encryption feature, the following describes which fields are encrypted for each sensitivity level selected per each account.
- High: Access-key ID, Secret Key
- Medium + High: Access-key ID, Secret Key
- Low + Medium + High: Access-key ID, Secret Key
...
| name | AccPerm |
|---|
Value: Deselected | Checkbox | Select this checkbox when you want to extend the maximum session duration of an IAM role defined in AWS. On selecting this checkbox, the cross-account IAM role is assumed with the maximum session duration defined for the IAM role.
| |||
Troubleshooting
| Multiexcerpt include macro | ||||||||
|---|---|---|---|---|---|---|---|---|
|
| Multiexcerpt macro | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
Account Permissions
|
...
Learn more about Setting Permissions and Permissions for the Amazon S3 |
...
ACL permissions
ACL permission | Corresponding access policy permissions when the ACL permission is granted on a bucket | Corresponding access policy permissions when the ACL permission is granted on an object |
|---|---|---|
|
|
|
|
In addition, when the grantee is the bucket owner, granting | Not applicable. |
|
|
|
|
|
|
| Equivalent to granting | Equivalent to granting |
| Insert excerpt | ||||||||
|---|---|---|---|---|---|---|---|---|
|