Two-Factor Auth Account
In this article
Overview
Use this account type to connect Binary Snaps with data sources that use Two-Factor Auth accounts. This account supports two factor authentication (2FA) for Security File Transfer Protocol (SFTP) to access SFTP. It uses two separate security layers of verification to grant access that include the Basic Auth (username/password) and the SSH Key (username/private key) methods.
Prerequisites
- Target FTP should be enabled with Two-Factor authentication.
- Valid username/password and SSH key with passphrase.
Limitations and Known Issues
None.
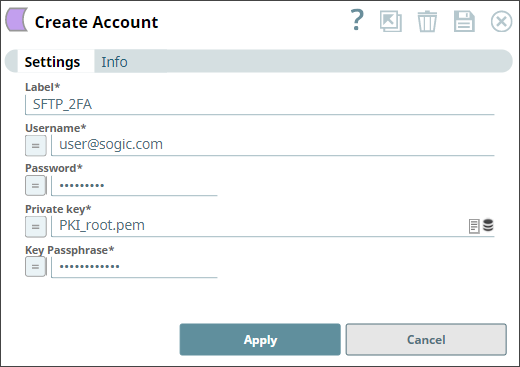
Account Settings
| Field Name | Field Type | Description |
|---|---|---|
Label* Default Value: N/A | String | Enter a unique label for the account. |
Username* Default Value: N/A | String/Expression | Enter a username for SSH authentication. |
Password* Default Value: N/A | String/Expression | Enter a password associated with the supplied account username. |
Private key* Default Value: N/A | String/Expression | Enter the private key part of SSH authentication. You can also upload the private key file to the SLDB by clicking the Upload icon. You can generate a private key using any SSH key generator. See Generate SSH Key Using PuTTY Key Generator for more information. Loading Loading |
Key Passphrase* Default Value: N/A | String/Expression | Enter the passphrase used to decrypt the private key. |
Account Encryption
Standard Encryption | If you are using Standard Encryption, follow the High sensitivity settings under Enhanced Encryption. |
| Enhanced Encryption | If the account you are using has the Enhanced Encryption feature, the account fields are encrypted for each sensitivity level as shown below:
|
Generating SSH Key Using PuTTY Key Generator
You can download the PuTTYgen application for Windows using this link.
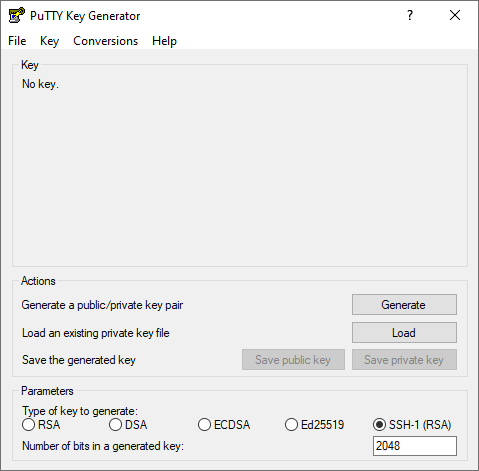
- Open the PuTTYgen application.
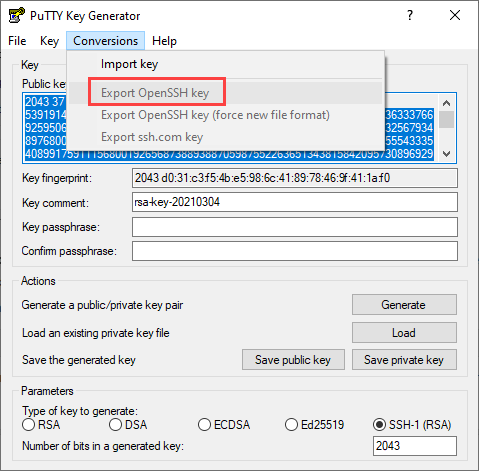
- Choose SSH-1 (RSA) key type under Parameters.
- Enter the required value in the Number of bits in a generate key field. (Default: 2048)
Click Generate that is adjacent to Generate a public/private key pair under Actions.
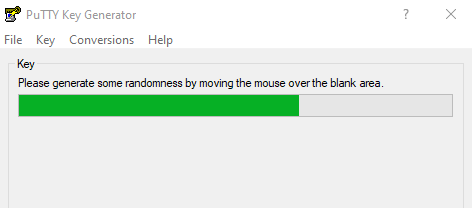
The PuTTY Key Generator uses mouse movements to generate a unique secure key. Move the mouse around till the progress bar fills up completely.
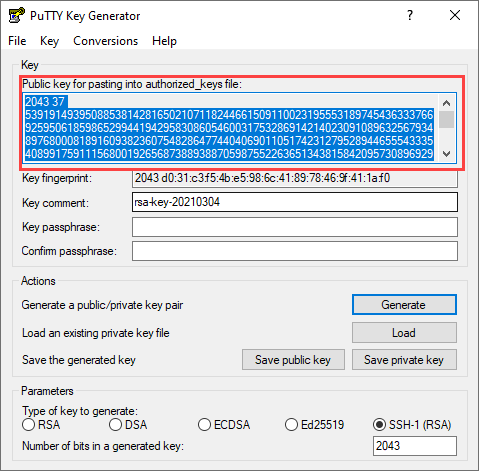
The utility generates the public and private keys.- Provide values in the Key comment and Key passphrase fields as required.
- Click Save public key and Save private key to save the private and public key (PPK) files to a secure and private location.
- Send the Public Key to the SFTP host.
- Store the keys and passphrase into the password/key vault.
The PuTTY Key Generator uses the PPK format for keys. If your SFTP client requires a standard OpenSSH key format, export the key by using Export OpenSSH Key on the Conversions menu.
Related Links
Have feedback? Email documentation@snaplogic.com | Ask a question in the SnapLogic Community
© 2017-2025 SnapLogic, Inc.